Certificate Abuse
https://viperone.gitbook.io/pentest-everything/everything/everything-active-directory/adcs/enumeration-certificate-authority
https://blog.csdn.net/PEIWIN/article/details/148265062
https://heartburn.dev/exploiting-active-directory-certificate-services-esc11-walkthrough/
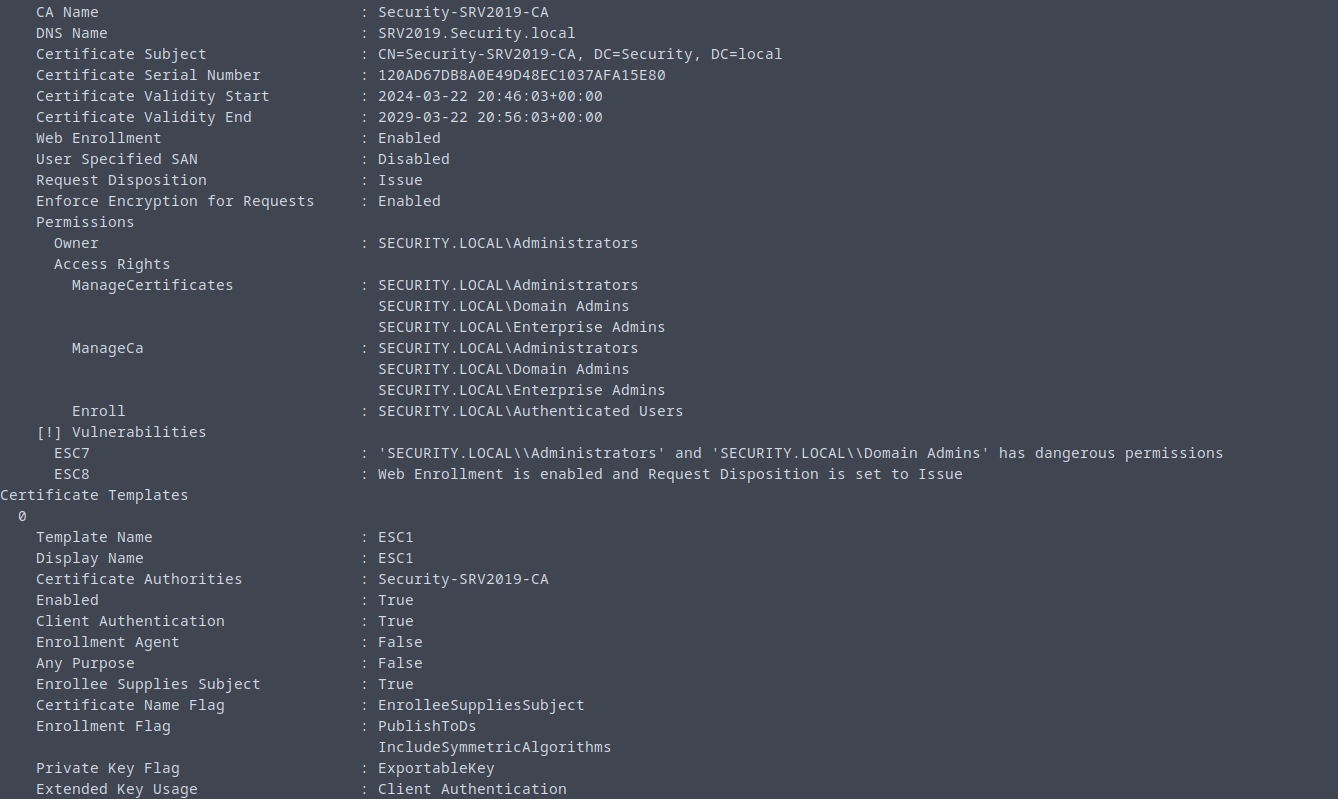
23.3.1 - Enumeration of the Certificate Authority
Get-ADObject -Filter * -SearchBase 'CN=Certification Authorities,CN=Public Key Services,CN=Services,CN=Configuration,DC=security,DC=local'
Get-ADObject -LDAPFilter '(objectclass=certificationAuthority)' -SearchBase 'CN=Configuration,DC=security,DC=local' | fl *
Also check with Certify
Certify.exe cas
Invoke-Certify cas
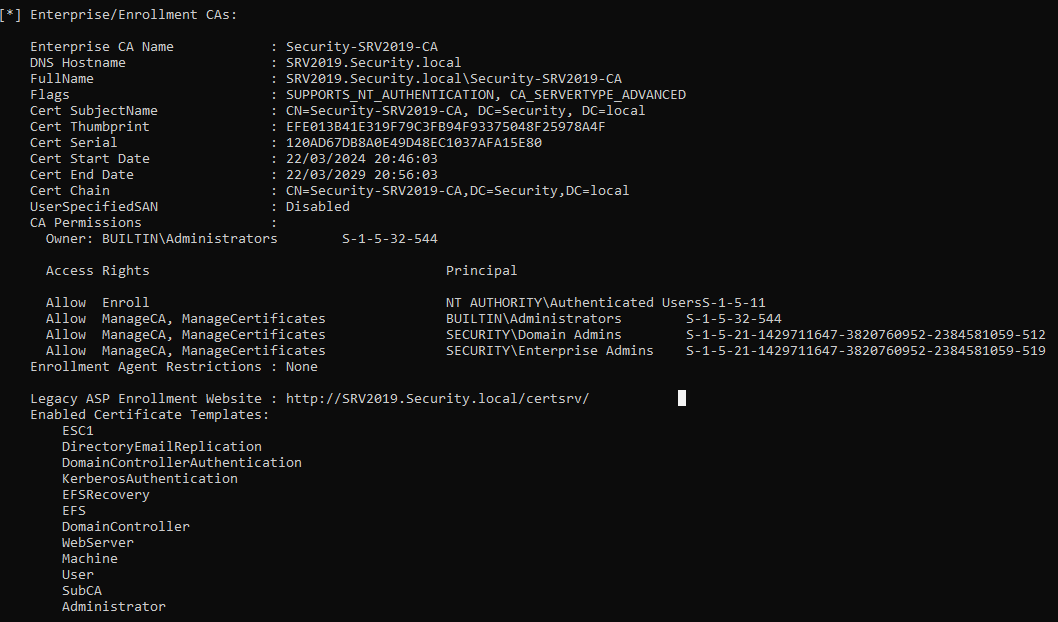
Also possible to run Certipy locally
https://github.com/ly4k/Certipy
certipy find -u <user> -p <password> -dc-ip 10.10.10.100 -stdout